I cook at a kitchen for our unhoused neighbors every month, and often am hit with last minute ingredient substitutions, donations of odd ingredients, and interesting food safety questions. Here are some rules for cooking more than 150 meals at…
“Yes, but how do I submit a comment on how unintuitive the comment submission process is?”
I’m smashblogging on a Saturday because I came across this story on FedScoop: https://fedscoop.com/white-house-launches-public-consultation-on-critical-ai-issues/ which discusses the Biden Administration’s Office of Science and Technology Policy’s launch of a public request for comment on their upcoming AI policy work. I wanted…
“If you can’t do something smart, do something right.”
Shepherd Book said that in Serenity, a lovely movie from 2005 that wrapped up the sadly-too-soon cancelled series Firefly. I use it a lot when institutional constraints and incentives stop me from doing the smartest and most effective thing possible.…
What is Montana, anyway?
I talked to a reporter yesterday about the recent TikTok ban legislation passed there, and explained some of the technical difficulties with enforcing any such ban. Hell, even the legislators themselves admit they can’t operationalize and enforce the ban. So,…
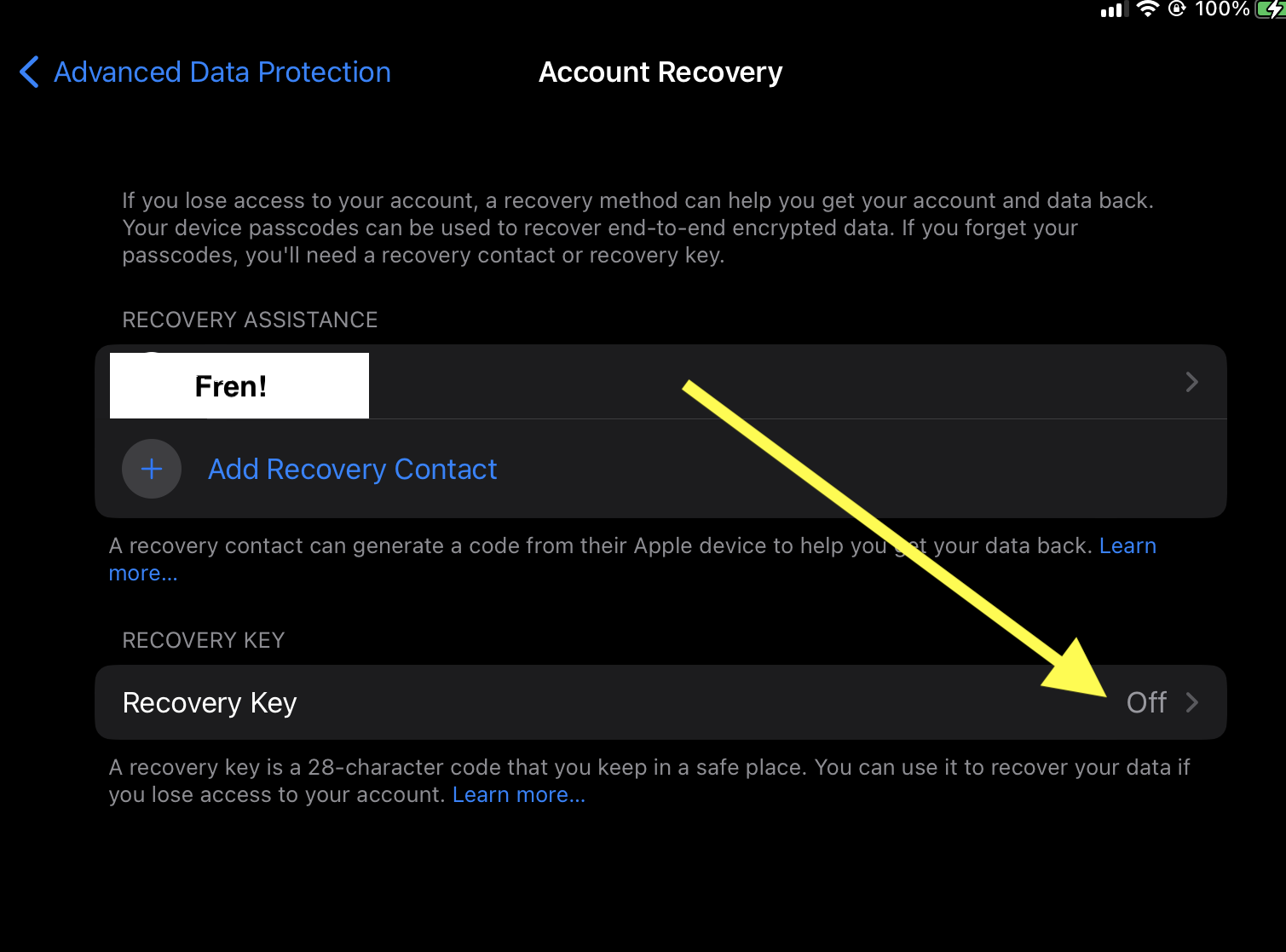
Troubleshooting Apple’s iCloud Advanced Data Protection
TL;DR: set your recovery key and contact, pick an iCloud device (I used my phone), log fully out of iCloud, and log back in. Try enabling ADP then. I tried a month ago to enable ADP on my iCloud account,…
That’s a nice cyber you’ve got there. Shame if something were to happen to it.
It should deeply concern us that cyber insurance is becoming less available. The CEO of Zurich Insurance (the company that denied Mondelez’s USD 100m claim after NotPetya on the grounds of it being warfare) says “What will become uninsurable is…
Contempt is the most dangerous emotion
There is an entire world of small and mid-sized businesses that are absolutely helpless in front of the kinds of attacks that we call “basic” in infosec. Invoice spearphishing, BEC, credential harvesting – these are the kinds of things we…
Why am I retiring from CTFs?
I’ve talked a lot about how I no longer do “fuzzy mentorship.” (If you haven’t heard the term, it’s generally seen as mentorship that focuses mostly on vague things like good vibes and is endeavored upon mostly for reasons of…
A Year of Reading Only New Things
It was March 4th, 2022. I already re-read all my comfort books over the last two years. In an effort to avoid becoming dull-witted, I’m going to only read new things for a year, between March 4th, 2022 and March…
An education-based approach to curbing CSAM production
Originally published in Brookings TechStream. March 17, 2022 Savannah Sly and Tarah Wheeler In recent weeks, a misguided legislative initiative to provide children with better protection online has gained momentum on Capitol Hill. In its current form, the Eliminating Abusive and Rampant Neglect of Interactive Technologies…